FBI Director Kash Patel's Emails Breached by Iran-Linked Hackers: A Deeper Look
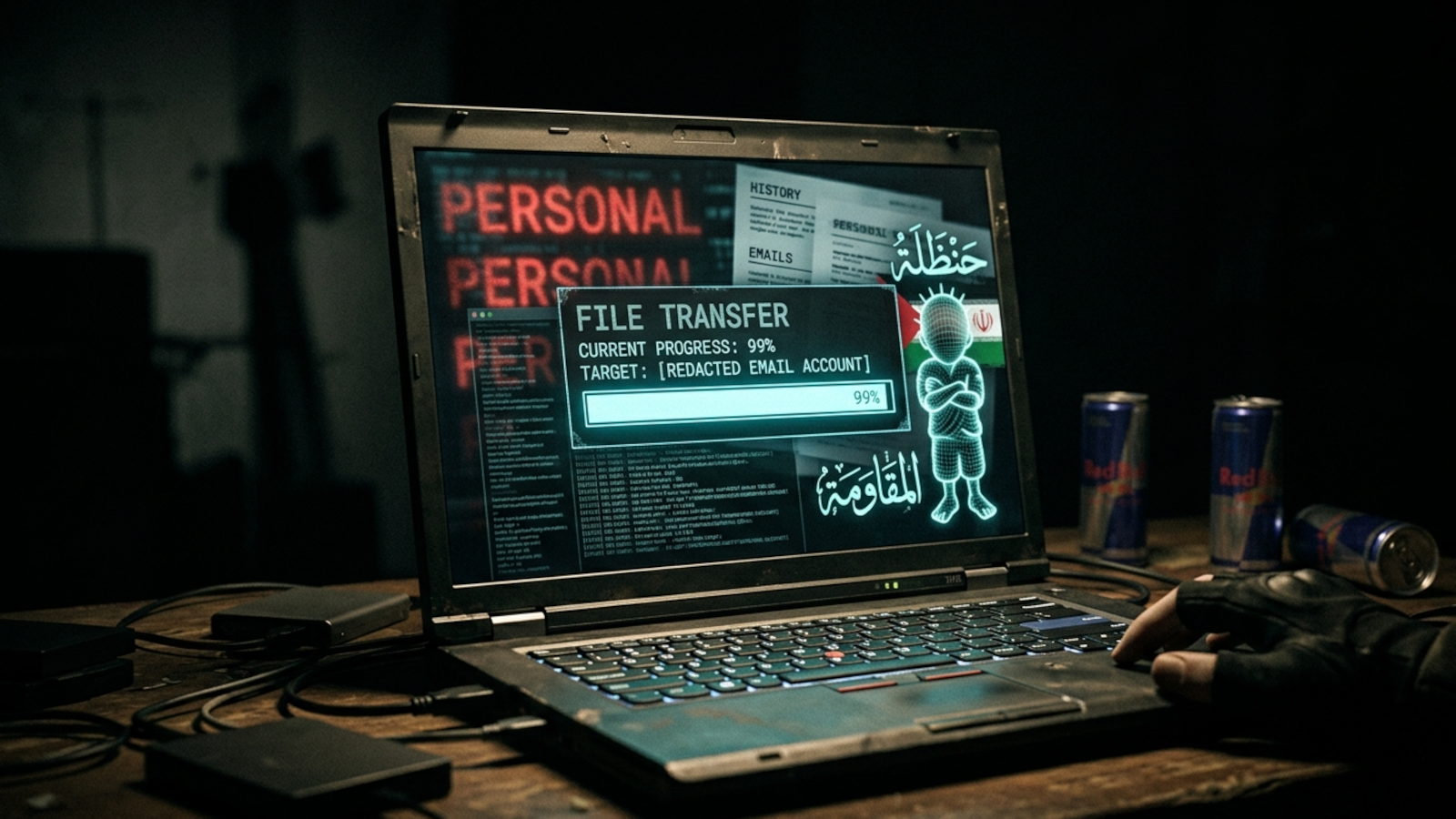
The digital world has once again been rocked by a high-profile cyber incident, with news emerging that FBI Director Kash Patel's personal email account fell victim to a breach by an Iran-linked group. This development underscores the persistent and evolving threat landscape faced by public figures, whose personal digital lives often become attractive targets for state-sponsored adversaries. The group, identifying itself as the Handala Hack Team, not only claimed responsibility but also publicly shared materials purportedly extracted from Mr. Patel's account, raising significant concerns about privacy, national security, and the methods employed by such malicious actors.
The Incident Unfolds: What Was Compromised?
The breach, confirmed by the FBI, involved the personal email account of Kash Patel. On a Friday, the Handala Hack Team broadcasted its claim, featuring a purported resume of Mr. Patel and several personal photos on its website. The accompanying statement ominously declared, "This is just our beginning." The FBI swiftly acknowledged awareness of "malicious actors" targeting Mr. Patel's email information, clarifying that the compromised data was "historical in nature and involves no government information." This distinction is crucial, suggesting that the breach may not have directly compromised sensitive government operations, but rather exposed personal details from an earlier period.
A preliminary review of the files, aided by cybersecurity experts, suggests the stolen emails and photos date primarily from around 2011 to 2022. These appear to encompass personal, business, and travel correspondence Mr. Patel had with various contacts. Photos circulated on social media, watermarked with the Handala group's logo, depict Mr. Patel in casual settings – by a vintage convertible, next to a jet, smoking cigars, or taking a selfie with a bottle of liquor. While the specific timing of the breach claimed by Handala remains somewhat ambiguous, cybersecurity experts like Cynthia Kaiser of Halcyon Ransomware Research Center posit that the released data likely originates from an older compromise, potentially "recycled" by the current group. This means the Handala Hack Team: Why Iran-Linked Group Leaked Kash Patel's Old Emails is a critical piece of the puzzle.
In response to the brazen attack, the FBI has taken a firm stance, offering a substantial reward of up to $10 million for information leading to the identification of members of the Handala group. This financial incentive highlights the seriousness with which the agency views such incursions, particularly when they target high-ranking officials.
The Handala Hack Team: Allegiances and Agendas
The Handala Hack Team is not an unknown entity in the realm of cyber warfare. This group has been consistently linked to the Islamic Republic of Iran, with the US Justice Department recently seizing several domain names it attributed to Handala. These domains, according to the department, were instrumental in "hacking schemes linked to the Islamic Republic of Iran," used for spreading "terrorist propaganda," conducting "attempted psychological operations targeting adversaries of the regime," and even claiming credit for other hacking activities while advocating for the killing of journalists.
Their statement accompanying the Kash Patel emails breach was laced with defiant rhetoric, boasting that the "so-called 'impenetrable' systems of the FBI were brought to their knees within hours." However, as experts have pointed out, the target was Mr. Patel's personal account, not the FBI's secure government systems. This distinction is crucial for understanding the nature of the attack. Dave Schroeder, Director of National Security Initiatives at the University of Wisconsin–Madison, notes that Handala frequently seeks this kind of access to prominent individuals and organizations precisely because it serves their interests to claim high-profile hacks, regardless of the actual level of sophistication involved in the initial breach.
The motivation behind such attacks is multifaceted. Beyond the immediate propaganda value and the satisfaction of embarrassing an adversary, these groups often aim to sow discord, erode public trust, and gather intelligence, even if it's "historical" personal information. The psychological impact of demonstrating the vulnerability of a powerful nation's officials should not be underestimated.
The Vulnerability of Personal Accounts: A Persistent Threat for Public Figures
The case of Kash Patel Email Hack: Exposing Officials' Personal Account Risks serves as a stark reminder of a critical cybersecurity paradox: while government systems are fortified with layers of advanced defenses, the personal digital lives of officials often present a comparatively softer target. As experts highlighted, personal email accounts typically "don't have the same level of protection and alerting as government systems." This makes them an attractive entry point for sophisticated actors, who may not require extraordinary technical prowess to exploit common vulnerabilities.
The "historical" nature of the data involved in the Kash Patel emails breach further complicates the picture. Many individuals, especially those who ascend to high-profile positions, may have personal accounts that predated their current roles, potentially lacking the robust security measures adopted later in their careers. Older accounts might be protected by weaker passwords, lack multi-factor authentication (MFA), or have been exposed in previous, lesser-known data breaches, making them susceptible to credential stuffing or other widely available hacking techniques. Once compromised, even years ago, this data can be held onto and weaponized at a politically opportune moment.
The implications of such breaches extend beyond immediate privacy concerns. For public figures, compromised personal information can be leveraged for blackmail, disinformation campaigns, or simply to undermine their credibility and authority. It provides adversaries with insights into their personal networks, habits, and past dealings, which can then be used for more targeted attacks or influence operations.
Safeguarding Digital Lives: Practical Advice for High-Profile Individuals
While the threat posed by state-sponsored groups is significant, there are actionable steps that high-profile individuals, and indeed everyone, can take to bolster their personal cybersecurity:
- Implement Multi-Factor Authentication (MFA) Everywhere: This is arguably the most crucial defense. Even if a password is stolen, MFA prevents unauthorized access by requiring a second verification step, like a code from a phone or a biometric scan.
- Practice Strong Password Hygiene: Use unique, complex passwords for every account. Consider a reputable password manager to help create and store them securely.
- Segregate Personal and Professional Digital Lives: Maintain entirely separate email addresses, devices, and online accounts for personal and professional use. Never mix sensitive government communications with personal platforms.
- Be Wary of Phishing Attempts: High-profile individuals are prime targets for sophisticated phishing schemes. Always scrutinize sender addresses, links, and attachments, and be skeptical of unsolicited communications.
- Regularly Review Account Security Settings: Periodically check and update security settings on all online accounts, including privacy controls and linked applications.
- Stay Informed About Past Breaches: Use services that notify you if your email addresses or other credentials have been compromised in known data breaches. This can help you proactively change passwords.
- Exercise Caution with Public Information: Be mindful of what is shared online, even on seemingly private social media. Adversaries can piece together vast amounts of information from disparate sources.
- Consider Professional Cybersecurity Consultation: For those in sensitive positions, engaging with cybersecurity experts to perform regular security audits and provide tailored advice is a sound investment.
Conclusion
The breach of Kash Patel's emails by an Iran-linked group serves as a powerful testament to the relentless nature of cyber threats. It highlights that no individual, regardless of their position, is immune to targeted attacks, especially when their personal digital footprint can be exploited. While the FBI assures no government information was compromised, the incident underscores the critical need for robust personal cybersecurity practices, particularly for those in the public eye. As the digital landscape continues to evolve, vigilance, strong security measures, and an awareness of the motivations of malicious actors are paramount to safeguarding privacy and national security.